Uncesscerary packages slow down system performance and take up storage space. If specific software isn't being used, then it's best to remove it, and doing so is easy.
In this tutorial, learn how to remove packages and uninstall dependencies from CentOS 7.
- Access to a user account with sudo or root privileges
- A terminal window or command line (Ctrl+Alt+F2)
- The YUM and RPM package managers, included by default
CentOS is an RHEL (Red Hat Enterprise Linux) distribution. Users rely on the RPM (Red-hat Package Manager) and YUM (The Yellowdog Updater, Modified) package manager.
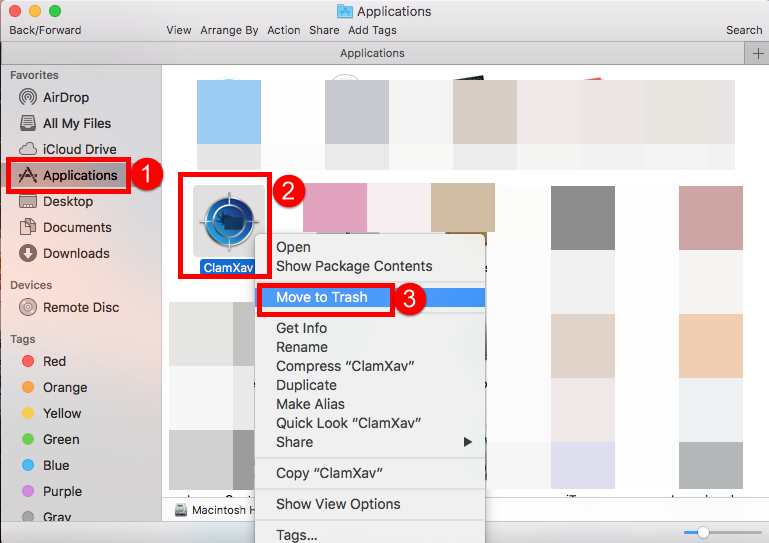
Given that it is a mac, you should just find the location of clamav application and delete it. To remove a package and erase all the unneeded dependencies use the following command: yum autoremove packagename Alternatively, you can alter the yum configuration file to automatically remove package dependencies when deleting a package with the yum remove or yum erase commands. Start by opening the yum.conf file with a text editor of your.
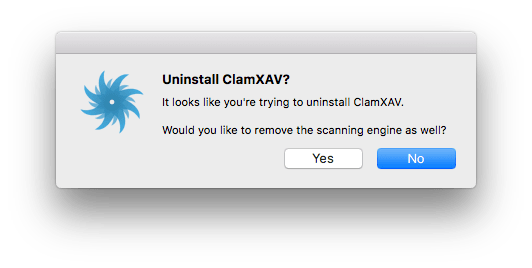
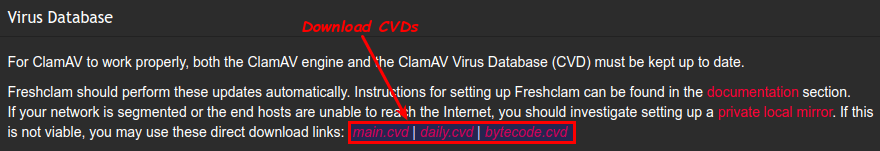
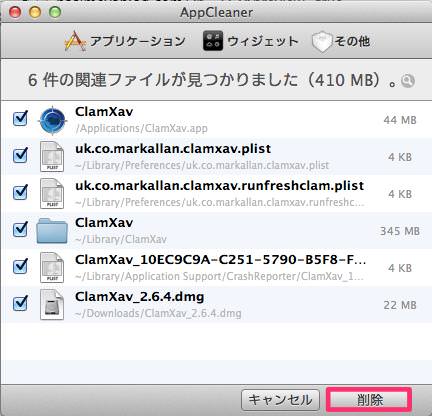
Tick Mac security off your to-do list today The ClamXAV scanner efficiently heads off malware and viruses in the workplace and can help you to comply with critical audit requirements and guidelines. Free trial Buy now. Clean up your classroom, common room or campus Keeping all your Macs clean and virus-free is remarkably simple with ClamXAV. Hi, I hope somebody can help me I need to un-install this program and get it off of my MacBook Pro computer.OS 10,9,5 I need the room on my SSD and I've been getting warnings. If you've installed an older version of ClamAV, uninstall the same, then compile and set up the latest version. For Windows, update the Microsoft packages first, then download the latest stable release and double-click the download to install the MSI package. As mentioned, ClamAV doesn't have many features compared to other.
To remove a package from CentOS, use the following yum commands:
OR
In the following example, we deleted the Apache web server package, filed under the name httpd.x86_64, using the yum command.
Before removing, the command prompt asks for the root (or sudo user) password, and confirmation that you want the software deleted.
Type in y (for yes) and press Enter. If you have changed your mind, press n (for no) and then Enter.
Finally, the output informs you that the process is complete and shows you which package has been deleted.
Note: Only root users and users added to the sudousers group have permission to install and remove packages in CentOS.
How to Remove Packages with Dependencies Using Yum
Package dependencies are binaries, libraries, and modules on which software rely on. When installing software, it will automatically download and store the required dependencies.
In most cases, deleting software from the local package manager will also erase its dependencies (unless other programs require them).
Still, there are instances in which these dependencies have to be removed manually.
To remove a package and erase all the unneeded dependencies use the following command:
Alternatively, you can alter the yum configuration file to automatically remove package dependencies when deleting a package with the yum remove or yum erase commands.
Start by opening the yum.conf file with a text editor of your choice:
Then, add the following line to the file:
Save and exit the file.
In case you need to delete a package but are unsure of its exact file name, you can use one of the following two commands:
OR
The output will list all installed packages with the specified phrase found in the file name.
As you can see in the image below, httpd appears in the following packages (and dependencies):
After you have the exact name of the package you want to erase, you can uninstall it from your CentOS system.
For more options on listing packages on CentOS read our detailed tutorial.
After reading this tutorial, you should now know how to remove packages and dependencies to free up space taken up by redundant programs.
You also know how quickly find specific packages or files you want to delete.
Next you should also read
Wget is a commonly used tool for downloading files in a command-line session. Not only is it fast and…
This guide will walk you through several methods for removing old or unwanted software from an Ubuntu Linux…
In Linux, a repository is a central database of software. Most modern Linux distributions have a central…
Managing a CentOS operating system often means knowing the software packages that are installed. This list…
How to remove redirects to s3.amazonaws[.]com from Mac computers
What is s3.amazonaws[.]com?
The s3.amazonaws[.]com website has been identified as proliferating a variety of unwanted and malicious content. It is hosted by Amazon AWS (Amazon Web Services), a legitimate service intended to provide various IT-related resources/functionalities, however, it is commonly misused by cyber criminals to host malicious sites. These web pages are then used to spread Potentially Unwanted Applications (PUAs) such as fake system cleaners/optimizers, adware, and browser hijackers, and also malware including ransomware, trojans, etc. This website generates redirects to various other rogue web pages. One researched variant of s3.amazonaws[.]com operates by promoting a fake Adobe Flash Player updater, which in turn can be used to infiltrate systems with the aforementioned content. People often enter s3.amazonaws[.]com unintentionally when they are redirected by intrusive advertisements or PUAs already infiltrated into the device.
The researched variant of s3.amazonaws[.]com displays a pop-up window, which claims that the latest updates to Flash Player are ready to install. Users are urged to click 'OK' to download the updates. The background reiterates that updates are ready for installation. It emphasises that the latest version must be installed for optimal performance. For example, to enable video and audio media and to play online games. Clicking any of the consent options will download the fraudulent updates. Installing them will not update Adobe Flash Player - instead, it will allow untrustworthy/malicious content onto the system. Fake software updaters are known to be used for PUA and malware proliferation. Trusting sites making similar claims and/or installing third party updaters is likely to lead to system infiltration and infections, and endanger user safety.
PUAs are one of the main causes of redirects to scam web pages. These apps can generate redirects to sale-based, untrustworthy, rogue, deceptive and malicious sites. They can also run intrusive advertisement campaigns. I.e., deliver unwanted, harmful ads that can diminish the browsing experience. The ads can cause redirects to likewise dangerous sites and stealthily download/install unwanted content. Other PUAs hijack browsers by making unauthorized changes, limiting/denying access to their settings and promoting fake search engines. Rogue system cleaners/optimizers are yet another type of unwanted application. These apps require activation to become operational (i.e., they require purchase to work), however, despite being activated, they remain nonoperational. Regardless of their specifications, most PUAs have data tracking capabilities, which they use to monitor browsing activity (browsing and search engine histories) and gather users' personal information (IP addresses, geolocations and other details). This private data is typically shared with third parties (often, cyber criminals) seeking to misuse it for profit. In summary, PUAs generate revenue for the developers and can cause system infiltration/infections, lead to serious privacy issues, financial loss and even identity theft. To ensure device and user safety, remove all suspicious applications and browser extensions/plug-ins immediately upon detection.
| Name | s3.amazonaws.com redirect virus |
| Threat Type | Phishing, Scam, Mac malware, Mac virus. |
| Fake Claim | Scam claims visitors need to install the latest version of Flash Player. |
| Detection Names (fake updater) | Avast (MacOS:Bundlore-CJ [Adw]), BitDefender (Adware.MAC.Bundlore.DXI), ClamAV (Unix.Malware.Agent-7425891-0), Kaspersky (Not-a-virus:HEUR:AdWare.OSX.Bnodlero.x), Full List (VirusTotal) |
| Promoted Unwanted Application | Scam promotes a fake software updater. |
| Symptoms | Your Mac becomes slower than normal, you see unwanted pop-up ads, you are redirected to dubious websites. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), fake Flash Player installers, torrent file downloads. |
| Damage | Internet browser tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites, loss of private information. |
| Malware Removal (Mac) | To eliminate possible malware infections, scan your Mac with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
bambootornado.pw, yourfine4upgradefree.best, and mainsiteofupgradenow.best are some examples of similar scams. These websites claim that visitors' Flash Players are outdated, but this simply a scam model. Deceptive web pages can make fraudulent claims about threats/issues on the device, offer 'amazing' deals, bogus prizes, and so on. These methods are social engineering and scare tactics. These schemes are used to encourage users into downloading and installing untrustworthy/malicious content, purchasing dubious/nonoperational products, making expensive calls, paying for bogus services, revealing personal and sensitive information (e.g. banking credentials), and for many other purposes. The underlying goal of these scams is to generate profit for their designers.
How did potentially unwanted applications install on my computer?
PUAs usually infiltrate devices without permission and downloaded/installed together with other products. This deceptive marketing technique of pre-packing regular software with unwanted or malicious content is called 'bundling'. Rushing download/installation processes (e.g. ignoring terms, skipping steps, etc.) increases the risk of inadvertently allowing bundled applications onto systems. Some of these applications have 'official' download pages, which are often promoted by deceptive/scam websites. When clicked, intrusive advertisements can execute scripts to stealthily download/install PUAs.
How to avoid installation of potentially unwanted applications
Content should be researched carefully prior to being downloaded/installed. Use only official and verified download sources. P2P sharing networks (BitTorrent, Gnutella, eMule, etc.), free file-hosting sites and other third party downloaders are untrustworthy and should be avoided. Products should be updated using functions/tools provided by legitimate developers, and not obtained from third parties. Treat download/Installation processes with caution. Read the terms, explore all available options, use the 'Custom/Advanced' settings and decline any offers to download/install supplementary apps, tools, features and so on. Intrusive ads typically seem normal and harmless, however, they can redirect to dubious web pages (e.g. gambling, pornography, adult-dating and others). If you experience ads/redirects of this kind, inspect the device and remove all suspect applications and/or browser extensions/plug-ins without delay. If your computer is already infected with PUAs, we recommend running a scan with Combo Cleaner Antivirus for macOS to automatically eliminate them.
Text presented in the pop-up window:
The Latest Version of Flash Player is Ready to Install.
Click ok to Download.

Text presented in the background of the web page:
Your Flash Player is ready to install
Run all your video, audio and games online
Update the latest version for optimal performance
Install
Appearance of the scam hosted on s3.amazonaws[.]com (GIF):
Screenshot of the fake Flash Player updater installation setup:
Another scam website hosted using s3.amazonaws.com service:
Text presented within this site:
Update Required
Update the latest version of Flash Player for Optimal Performance.
UPDATE NOW
Appearance of this site (GIF):
Another pop-up scam promoted using Amazon AWS service:
Text presented within this site:
Software Update
Clamav Download For Windows 10
New update is available for your computer.
Your OS might need Flash Player for HD Support.
Please update your Flash Player to continue.
Clamav Windows
Install Name Version Size
V Media Player Mac OS X 0.6M
Note: The version of your player on your system downs not include the latest updates.
To continue, download an updated version.
Installing takes under a minute - No restart is required.
Installer promoted via this scam page:
Yet another pop-up scam promoted using Amazon AWS service:
Text presented within this page:
Flash Player update is available for your computer
Older versions of Flash Player are vulnerable to online threats, you'll want to make sure you're always using the most recent version. If you're not running the most recent version, you might see an error message instead of your content.
Flash Player supports several data formats, including XML, JSON, AMF, and SWF. Multimedia formats supported by the Flash Player include mp3, FLV, PNG, JPEG, GIF, and RTMP, among others.
Version Update: The newest version of Flash Player enables greater security and privacy controls with protected HTTPS Dynamic Streaming (HDS). Other features include webcam support, accelerated graphics rendering, multithread video decoding, and improved software for high-end performance.
Update Now
Terms and Conditions Privacy Policy
Screenshot of a deceptive installer promoted via this scam:
Instant automatic Mac malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of Mac malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner for MacBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Quick menu:
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your 'Applications' folder:
Click the Finder icon. In the Finder window, select 'Applications'. In the applications folder, look for 'MPlayerX','NicePlayer', or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Remove s3.amazonaws.com redirect virus related files and folders:
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
Check for adware-generated files in the /Library/LaunchAgents folder:
In the Go to Folder... bar, type: /Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware generated files in the /Library/Application Support folder:
In the Go to Folder... bar, type: /Library/Application Support
In the 'Application Support' folder, look for any recently-added suspicious folders. For example, 'MplayerX' or 'NicePlayer', and move these folders to the Trash.
Check for adware-generated files in the ~/Library/LaunchAgents folder:
In the Go to Folder bar, type: ~/Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware-generated files in the /Library/LaunchDaemons folder:
In the Go to Folder... bar, type: /Library/LaunchDaemons
In the 'LaunchDaemons' folder, look for recently-added suspicious files. For example 'com.aoudad.net-preferences.plist', 'com.myppes.net-preferences.plist', 'com.kuklorest.net-preferences.plist', 'com.avickUpd.plist', etc., and move them to the Trash.
Clamav For Linux
Scan your Mac with Combo Cleaner:
If you have followed all the steps in the correct order you Mac should be clean of infections. To be sure your system is not infected run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file double click combocleaner.dmg installer, in the opened window drag and drop Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates it's virus definition database and click 'Start Combo Scan' button.
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays 'no threats found' - this means that you can continue with the removal guide, otherwise it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
s3.amazonaws.com redirect virus removal from Internet browsers:
Remove malicious extensions from Safari:
Remove s3.amazonaws.com redirect virus related Safari extensions:
Open Safari browser, from the menu bar, select 'Safari' and click 'Preferences...'.
In the preferences window, select 'Extensions' and look for any recently-installed suspicious extensions. When located, click the 'Uninstall' button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
Remove malicious plug-ins from Mozilla Firefox:
Remove s3.amazonaws.com redirect virus related Mozilla Firefox add-ons:
Open your Mozilla Firefox browser. At the top right corner of the screen, click the 'Open Menu' (three horizontal lines) button. From the opened menu, choose 'Add-ons'.
After you have the exact name of the package you want to erase, you can uninstall it from your CentOS system.
For more options on listing packages on CentOS read our detailed tutorial.
After reading this tutorial, you should now know how to remove packages and dependencies to free up space taken up by redundant programs.
You also know how quickly find specific packages or files you want to delete.
Next you should also read
Wget is a commonly used tool for downloading files in a command-line session. Not only is it fast and…
This guide will walk you through several methods for removing old or unwanted software from an Ubuntu Linux…
In Linux, a repository is a central database of software. Most modern Linux distributions have a central…
Managing a CentOS operating system often means knowing the software packages that are installed. This list…
How to remove redirects to s3.amazonaws[.]com from Mac computers
What is s3.amazonaws[.]com?
The s3.amazonaws[.]com website has been identified as proliferating a variety of unwanted and malicious content. It is hosted by Amazon AWS (Amazon Web Services), a legitimate service intended to provide various IT-related resources/functionalities, however, it is commonly misused by cyber criminals to host malicious sites. These web pages are then used to spread Potentially Unwanted Applications (PUAs) such as fake system cleaners/optimizers, adware, and browser hijackers, and also malware including ransomware, trojans, etc. This website generates redirects to various other rogue web pages. One researched variant of s3.amazonaws[.]com operates by promoting a fake Adobe Flash Player updater, which in turn can be used to infiltrate systems with the aforementioned content. People often enter s3.amazonaws[.]com unintentionally when they are redirected by intrusive advertisements or PUAs already infiltrated into the device.
The researched variant of s3.amazonaws[.]com displays a pop-up window, which claims that the latest updates to Flash Player are ready to install. Users are urged to click 'OK' to download the updates. The background reiterates that updates are ready for installation. It emphasises that the latest version must be installed for optimal performance. For example, to enable video and audio media and to play online games. Clicking any of the consent options will download the fraudulent updates. Installing them will not update Adobe Flash Player - instead, it will allow untrustworthy/malicious content onto the system. Fake software updaters are known to be used for PUA and malware proliferation. Trusting sites making similar claims and/or installing third party updaters is likely to lead to system infiltration and infections, and endanger user safety.
PUAs are one of the main causes of redirects to scam web pages. These apps can generate redirects to sale-based, untrustworthy, rogue, deceptive and malicious sites. They can also run intrusive advertisement campaigns. I.e., deliver unwanted, harmful ads that can diminish the browsing experience. The ads can cause redirects to likewise dangerous sites and stealthily download/install unwanted content. Other PUAs hijack browsers by making unauthorized changes, limiting/denying access to their settings and promoting fake search engines. Rogue system cleaners/optimizers are yet another type of unwanted application. These apps require activation to become operational (i.e., they require purchase to work), however, despite being activated, they remain nonoperational. Regardless of their specifications, most PUAs have data tracking capabilities, which they use to monitor browsing activity (browsing and search engine histories) and gather users' personal information (IP addresses, geolocations and other details). This private data is typically shared with third parties (often, cyber criminals) seeking to misuse it for profit. In summary, PUAs generate revenue for the developers and can cause system infiltration/infections, lead to serious privacy issues, financial loss and even identity theft. To ensure device and user safety, remove all suspicious applications and browser extensions/plug-ins immediately upon detection.
| Name | s3.amazonaws.com redirect virus |
| Threat Type | Phishing, Scam, Mac malware, Mac virus. |
| Fake Claim | Scam claims visitors need to install the latest version of Flash Player. |
| Detection Names (fake updater) | Avast (MacOS:Bundlore-CJ [Adw]), BitDefender (Adware.MAC.Bundlore.DXI), ClamAV (Unix.Malware.Agent-7425891-0), Kaspersky (Not-a-virus:HEUR:AdWare.OSX.Bnodlero.x), Full List (VirusTotal) |
| Promoted Unwanted Application | Scam promotes a fake software updater. |
| Symptoms | Your Mac becomes slower than normal, you see unwanted pop-up ads, you are redirected to dubious websites. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), fake Flash Player installers, torrent file downloads. |
| Damage | Internet browser tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites, loss of private information. |
| Malware Removal (Mac) | To eliminate possible malware infections, scan your Mac with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
bambootornado.pw, yourfine4upgradefree.best, and mainsiteofupgradenow.best are some examples of similar scams. These websites claim that visitors' Flash Players are outdated, but this simply a scam model. Deceptive web pages can make fraudulent claims about threats/issues on the device, offer 'amazing' deals, bogus prizes, and so on. These methods are social engineering and scare tactics. These schemes are used to encourage users into downloading and installing untrustworthy/malicious content, purchasing dubious/nonoperational products, making expensive calls, paying for bogus services, revealing personal and sensitive information (e.g. banking credentials), and for many other purposes. The underlying goal of these scams is to generate profit for their designers.
How did potentially unwanted applications install on my computer?
PUAs usually infiltrate devices without permission and downloaded/installed together with other products. This deceptive marketing technique of pre-packing regular software with unwanted or malicious content is called 'bundling'. Rushing download/installation processes (e.g. ignoring terms, skipping steps, etc.) increases the risk of inadvertently allowing bundled applications onto systems. Some of these applications have 'official' download pages, which are often promoted by deceptive/scam websites. When clicked, intrusive advertisements can execute scripts to stealthily download/install PUAs.
How to avoid installation of potentially unwanted applications
Content should be researched carefully prior to being downloaded/installed. Use only official and verified download sources. P2P sharing networks (BitTorrent, Gnutella, eMule, etc.), free file-hosting sites and other third party downloaders are untrustworthy and should be avoided. Products should be updated using functions/tools provided by legitimate developers, and not obtained from third parties. Treat download/Installation processes with caution. Read the terms, explore all available options, use the 'Custom/Advanced' settings and decline any offers to download/install supplementary apps, tools, features and so on. Intrusive ads typically seem normal and harmless, however, they can redirect to dubious web pages (e.g. gambling, pornography, adult-dating and others). If you experience ads/redirects of this kind, inspect the device and remove all suspect applications and/or browser extensions/plug-ins without delay. If your computer is already infected with PUAs, we recommend running a scan with Combo Cleaner Antivirus for macOS to automatically eliminate them.
Text presented in the pop-up window:
The Latest Version of Flash Player is Ready to Install.
Click ok to Download.
Text presented in the background of the web page:
Your Flash Player is ready to install
Run all your video, audio and games online
Update the latest version for optimal performance
Install
Appearance of the scam hosted on s3.amazonaws[.]com (GIF):
Screenshot of the fake Flash Player updater installation setup:
Another scam website hosted using s3.amazonaws.com service:
Text presented within this site:
Update Required
Update the latest version of Flash Player for Optimal Performance.
UPDATE NOW
Appearance of this site (GIF):
Another pop-up scam promoted using Amazon AWS service:
Text presented within this site:
Software Update
Clamav Download For Windows 10
New update is available for your computer.
Your OS might need Flash Player for HD Support.
Please update your Flash Player to continue.
Clamav Windows
Install Name Version Size
V Media Player Mac OS X 0.6M
Note: The version of your player on your system downs not include the latest updates.
To continue, download an updated version.
Installing takes under a minute - No restart is required.
Installer promoted via this scam page:
Yet another pop-up scam promoted using Amazon AWS service:
Text presented within this page:
Flash Player update is available for your computer
Older versions of Flash Player are vulnerable to online threats, you'll want to make sure you're always using the most recent version. If you're not running the most recent version, you might see an error message instead of your content.
Flash Player supports several data formats, including XML, JSON, AMF, and SWF. Multimedia formats supported by the Flash Player include mp3, FLV, PNG, JPEG, GIF, and RTMP, among others.
Version Update: The newest version of Flash Player enables greater security and privacy controls with protected HTTPS Dynamic Streaming (HDS). Other features include webcam support, accelerated graphics rendering, multithread video decoding, and improved software for high-end performance.
Update Now
Terms and Conditions Privacy Policy
Screenshot of a deceptive installer promoted via this scam:
Instant automatic Mac malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of Mac malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner for MacBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Quick menu:
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your 'Applications' folder:
Click the Finder icon. In the Finder window, select 'Applications'. In the applications folder, look for 'MPlayerX','NicePlayer', or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Remove s3.amazonaws.com redirect virus related files and folders:
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
Check for adware-generated files in the /Library/LaunchAgents folder:
In the Go to Folder... bar, type: /Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware generated files in the /Library/Application Support folder:
In the Go to Folder... bar, type: /Library/Application Support
In the 'Application Support' folder, look for any recently-added suspicious folders. For example, 'MplayerX' or 'NicePlayer', and move these folders to the Trash.
Check for adware-generated files in the ~/Library/LaunchAgents folder:
In the Go to Folder bar, type: ~/Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware-generated files in the /Library/LaunchDaemons folder:
In the Go to Folder... bar, type: /Library/LaunchDaemons
In the 'LaunchDaemons' folder, look for recently-added suspicious files. For example 'com.aoudad.net-preferences.plist', 'com.myppes.net-preferences.plist', 'com.kuklorest.net-preferences.plist', 'com.avickUpd.plist', etc., and move them to the Trash.
Clamav For Linux
Scan your Mac with Combo Cleaner:
If you have followed all the steps in the correct order you Mac should be clean of infections. To be sure your system is not infected run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file double click combocleaner.dmg installer, in the opened window drag and drop Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates it's virus definition database and click 'Start Combo Scan' button.
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays 'no threats found' - this means that you can continue with the removal guide, otherwise it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
s3.amazonaws.com redirect virus removal from Internet browsers:
Remove malicious extensions from Safari:
Remove s3.amazonaws.com redirect virus related Safari extensions:
Open Safari browser, from the menu bar, select 'Safari' and click 'Preferences...'.
In the preferences window, select 'Extensions' and look for any recently-installed suspicious extensions. When located, click the 'Uninstall' button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
Remove malicious plug-ins from Mozilla Firefox:
Remove s3.amazonaws.com redirect virus related Mozilla Firefox add-ons:
Open your Mozilla Firefox browser. At the top right corner of the screen, click the 'Open Menu' (three horizontal lines) button. From the opened menu, choose 'Add-ons'.
Choose the 'Extensions' tab and look for any recently-installed suspicious add-ons. When located, click the 'Remove' button next to it/them. Note that you can safely uninstall all extensions from your Mozilla Firefox browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Remove malicious extensions from Google Chrome:
Remove s3.amazonaws.com redirect virus related Google Chrome add-ons:
Open Google Chrome and click the 'Chrome menu' (three horizontal lines) button located in the top-right corner of the browser window. From the drop-down menu, choose 'More Tools' and select 'Extensions'.
Clamav Mac Uninstaller
In the 'Extensions' window, look for any recently-installed suspicious add-ons. When located, click the 'Trash' button next to it/them. Note that you can safely uninstall all extensions from your Google Chrome browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
